We blogged about sharing services in a decentralised business context recently, and explained why we think why these should be IT-Based for speedy delivery. This is not to say that all shared services projects worldwide have been resounding successes. This is often down to the lack of a solid business case up front. We decided to lay out the logic behind this process.
Management Overview ? The overview includes a clear definition of why the current situation is unacceptable, the anticipated benefits of sharing, and an implementation plan were it to go ahead. The project should not proceed until the stakeholders have considered and agreed on this.
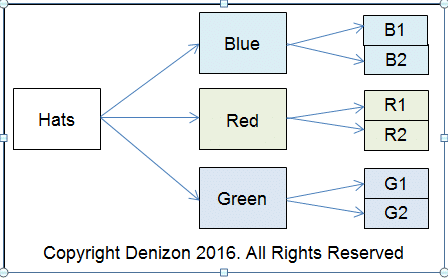
Alternatives Considered ? The next stage is to get closer to the other options in order to determine whether an alternative might perhaps be preferable. Substitutes for shared services are often doing nothing, improving the current method, and outsourcing the service to a third party.
The Bottom Line in Business ? Sharing services comes at an initial cost of infrastructure changes, and the impact on human capital (the latter deserves its own blog). The following need careful consideration from the financial angle:
Numbers to Work Through
- Manpower to design and roll the project out in parallel with the existing organisation.
- Capital for creating facilities at the central point including civil works, furniture and equipment and IT infrastructure.
- The costs of travel, feeding and accommodation. These can be significant depending on the time that implementation takes.
- The opportunity loss of diverting key staff – and the cost of temporary replacements – if appointing line staff to the project team.
- Crystal-clear project metrics including (a) the direct, realisable savings (b) the medium and long-term effects on profit and (c) where to deploy the savings
Risk Management
Shared services projects don’t go equally smoothly, although planning should reduce the risk to manageable levels. Nonetheless it is important to imagine potential snags, decide how to mitigate them and what the cost might be.
We believe in implementing shared services on a pilot basis in the business unit that eventually provides them. We recommend building these out to other branches only when new processes are working smoothly.
Moving On From a Decision
We recommend you revisit your management overview, the logic behind it, the assumptions you made, and the costs and benefits you envisage before deciding to go ahead
The final step in proving a business case is doable should be fleshing out your roadmap into a detailed operations plan with dependencies on a spreadsheet.